In the first part of this series exploring trust in the digital age, we looked at how in a legal setting digital documents challenge traditional assumptions of authenticity and evidential weight. In this second piece, we turn to the next frontier of everyday communication: chat messages.
Chat messages from platforms such as WhatsApp, Signal and Telegram frequently become the subject of legal disputes when they are the primary record of decisions, agreements, or instructions. Issues often arise over authenticity, completeness, or context, particularly when messages are edited, deleted, or presented as selective screenshots.
For lawyers handling these investigations, chat data presents a markedly different evidential landscape from documents. Messages are typically informal, rapid, and technically complex: a single conversation may involve multiple participants, devices, time zones, and system processes that influence how the information is stored and displayed. What appears on screen as a simple exchange is often just a partial reconstruction of a much richer underlying record.
In this second article, Jordan Hare and Katarina Zotovic on S-RM’s Digital Forensics team explore how chat communications present unique evidential challenges and what this means for assessing their authenticity and reliability.
Is a screenshot definitive?
In many investigations, chat evidence is initially presented in the form of screenshots. From a practical standpoint, this is often driven by convenience. Clients may be reluctant to surrender devices for forensic examination due to the disruption involved, the sensitivity of personal data stored on those devices, or the time required to perform a full forensic extraction. A screenshot, by contrast, appears to offer a simple alternative: it captures exactly what the user sees on their screen and presents it in a format that is immediately readable and easy to interpret.
At first glance, screenshots can appear highly persuasive. A messaging interface displays chats in a familiar conversational format, complete with timestamps, participant names, and visual indicators that resemble the live application environment. Compared with raw data exports or spreadsheets of extracted messages, screenshots may feel more intuitive and accessible, particularly for individuals who are not accustomed to reviewing technical datasets.
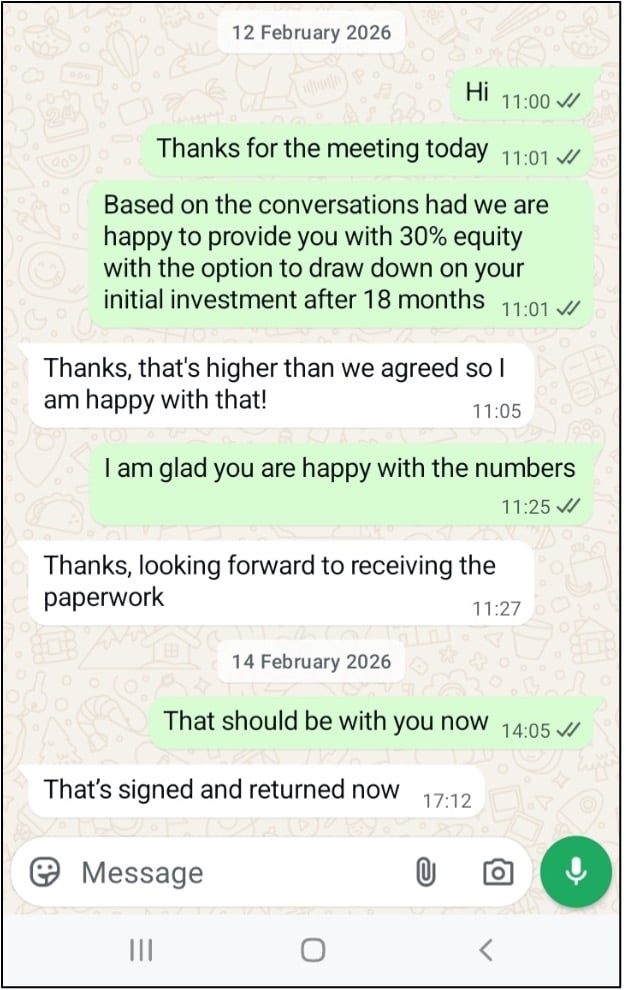
Consider Figure 1 below - the screenshot appears to be a series of messages exchanged between two users on WhatsApp. From an evidential perspective, the conversation appears straightforward: the participants are visible, the messages are ordered chronologically, and the timestamps indicate when the exchange took place. On its face, the image provides a clear narrative of communication between the two individuals.
Figure 1 Screenshot disclosed by Party A
Now consider Figure 2 below.
Figure 2 Screenshot disclosed by Party B
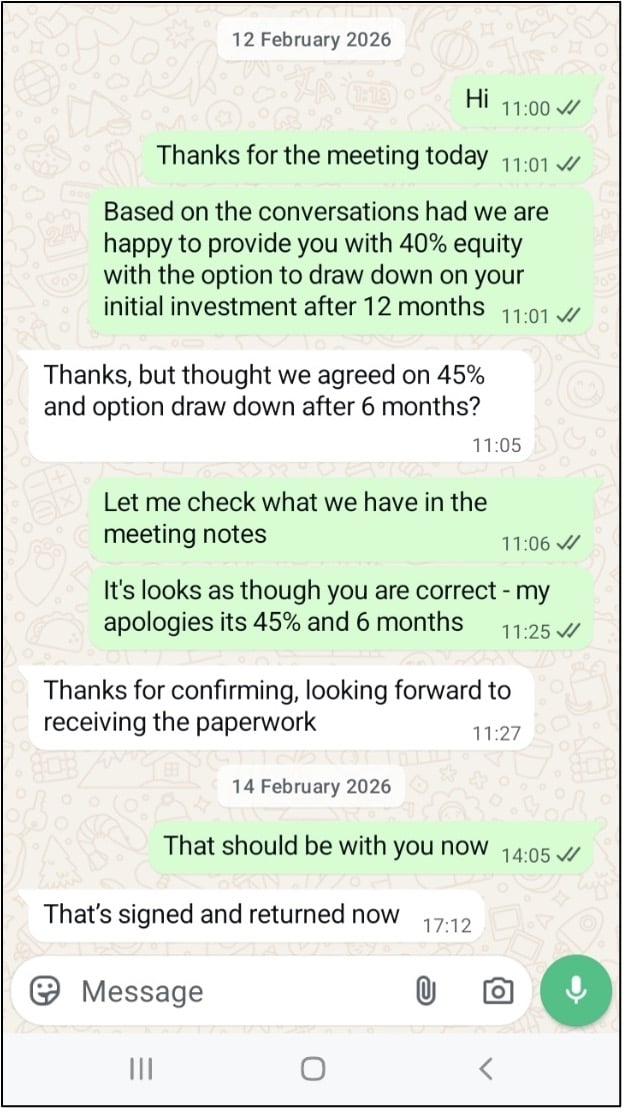
Both screenshots appear legitimate, yet their meanings are entirely different. This is where many legal disputes arise: two seemingly genuine sets of screenshots are presented, each convincing to the casual observer, but contentious in their veracity. So which of the two screenshots above is an original, and which is falsified?
Following the disclosure of the screenshots, legal counsel has grounds to request access to the devices on which these chats originated, providing forensic examiners with the original data sources to investigate authenticity. After cross-referencing device data, chat logs, metadata, and visual elements, forensic examiners determine that Figure 2 is the authentic screenshot. The metadata associated with Figure 2 aligns with the expected timestamps and app version, matching the actual system data and device settings at the time of the conversation. Cross-referencing the chat logs from the device and cloud backups confirms that the messages in Figure 2 were indeed exchanged, further verifying its authenticity.
When a screenshot is provided in isolation, the image itself effectively becomes the sole source of evidence for that conversation, and one that – as illustrated above – can be easily manipulated. This example raises important questions that legal experts and forensic examiners must consider when evaluating chat evidence: who created the screenshots, when were they captured, and from what underlying data source were they generated? Without access to the original message databases stored on the device or within the messaging application’s backups, it is often difficult to answer these questions with certainty. However, when two different sets of screenshots are provided by opposing sides, legal teams have a strong basis to request access to the original devices for comprehensive forensic investigation.
Can screenshots still be useful?
Despite their limitations, screenshots can still play a useful role in an investigation when considered alongside other sources of evidence. While a screenshot may not reliably prove the authenticity of the messages it displays, it can nevertheless provide valuable starting points for further inquiry. In many cases, the image file itself contains metadata that may offer insight into how and when it was created.
For instance, screenshots often retain metadata generated by the device on which they were captured. This can include information such as the device model, operating system, file creation timestamp, and sometimes details relating to the application used at the time. Such metadata can then serve as the foundation for requesting additional disclosure, like the original device used for capturing the screenshot. Timestamps can further establish a timeline, providing insights into how the screenshot aligns with other relevant events in the case.
Although a screenshot alone does not verify the accuracy of the messages it displays, it can support and advance an investigation.
Conclusion
The use of screenshots as evidence presents significant challenges in terms of reliability and authenticity. While they may appear convincing at first glance, the ease with which screenshots can be falsified or manipulated can weaken their reliability as an evidence source. Without supporting evidence, such as forensic extractions of devices or access to cloud data, the screenshots alone can mislead investigators and counsel alike.
While screenshots may serve as a convenient and accessible form of evidence, their ease of manipulation makes them less reliable than other types of digital records. For forensic investigators and legal professionals, it is crucial to approach screenshots with caution and seek additional corroborating evidence whenever possible. Only through a comprehensive analysis of all available data, including screenshots, metadata, chat databases, and system processes of original devices can the true authenticity of chat communications be accurately assessed.





